Blog
Biometric Security and Identity Orchestration
Biometric Security and Identity Orchestration
AI enables organizations to have 24/7 surveillance and proactive cyber threat hunting. This pillar focuses on 'Secure AI Ecosystems' and biometric protection. Sub-topic clusters include intelligent microphone arrays for secure spatial audio, AI-powered microelectrode arrays for identity verification, and centralizing control across third-party AI applications.
Why Biometric AI is Essential for Zero-Trust Architectures
Biometric AI provides the continuous, context-aware authentication required to enforce true zero-trust principles, moving beyond perimeter-based security.
How AI-Powered Liveness Detection Makes Passwords Obsolete
Advanced AI models that detect spoofing in real-time are the final nail in the coffin for static, knowledge-based authentication like passwords.
The Hidden Risk of Biometric Data Poisoning Attacks
Adversarial attacks that corrupt training data pose an existential threat to biometric AI systems, requiring robust ModelOps and anomaly detection.
Why Edge AI is Critical for Real-Time Biometric Security
Deploying biometric models on edge devices like NVIDIA Jetson reduces latency for threat response and enhances data privacy by minimizing cloud exposure.
The Compliance Gap in Current Biometric AI Systems
Most biometric platforms lack the explainability and governance frameworks needed for compliance with regulations like the EU AI Act, creating significant legal risk.
Why Federated Learning is Risky for Biometric Models
While federated learning protects raw data, it introduces vulnerabilities to model inversion and poisoning attacks that can compromise the entire decentralized system.
The Strategic Cost of Outsourcing Your Biometric AI Stack
Reliance on third-party APIs for core identity functions creates a critical dependency, limiting customization and obscuring security postures.
How AI-Powered Voiceprint Analysis Prevents Fraud
Advanced voice AI analyzes hundreds of acoustic features to create unforgeable voiceprints, becoming a frontline defense against synthetic voice and deepfake fraud.
The Model Drift Problem in Static Biometric AI
Biometric traits and spoofing techniques evolve, requiring continuous model retraining and MLOps pipelines to prevent accuracy decay over time.
Why Synthetic Data Fails for Biometric Model Training
AI-generated synthetic data lacks the nuanced, adversarial edge cases found in real-world biometric data, creating models vulnerable to novel spoofs.
The Latency Cost of Cloud-Based Biometric Inference
Round-trip latency to cloud AI services like Google Vertex AI introduces critical delays in authentication, making edge deployment a security imperative.
How Intelligent Microphone Arrays Enable Secure Spatial Audio
AI-driven beamforming and source separation in microphone arrays allow for precise voice capture and location tracking, securing physical perimeters.
Why Explainable AI is Non-Negotiable for Biometric Decisions
Unexplainable biometric rejections create user friction and legal liability, necessitating techniques like SHAP and LIME for auditability.
The Architectural Cost of Siloed Biometric Systems
Disconnected facial, voice, and behavioral biometric systems create security gaps and poor user experience; a unified orchestration layer is required.
How AI-Powered Gait Analysis Moves Beyond Surveillance
Computer vision models analyzing gait patterns offer continuous, non-intrusive authentication in sensitive areas where other biometrics are impractical.
The Vendor Lock-in Risk of Proprietary Biometric Algorithms
Dependence on a vendor's closed-source AI models creates switching costs and obscures model performance, hindering long-term security strategy.
Why Behavioral Biometrics Alone Fail Against Insider Threats
Models based solely on keystroke dynamics or mouse movements can be mimicked by determined insiders, requiring fusion with physiological traits.
The Technical Debt of Bolted-On Biometric AI Modules
Integrating point biometric solutions into legacy IAM systems creates fragile, unmaintainable architectures that are expensive to scale and secure.
How Privacy-Enhancing Tech Secures Biometric AI Processing
Techniques like homomorphic encryption and secure multi-party computation allow biometric matching without exposing raw template data, aligning with privacy laws.
Why Centralized Control of AI Applications is a CTO Imperative
A centralized AI security platform is essential for governing permissions, monitoring third-party AI app risks, and maintaining a unified security posture.
The False Promise of Multimodal Biometric Fusion
Simply combining multiple biometric signals without a sophisticated AI fusion strategy can increase complexity and attack surfaces without improving security.
How AI Enables Continuous Authentication Beyond the Login
Agentic AI systems continuously analyze behavioral and contextual signals post-login, automatically triggering step-up authentication for anomalous activity.
The Data Sovereignty Risk of Global Biometric Cloud Providers
Storing biometric templates with hyperscalers like AWS or Azure can violate data residency laws, pushing organizations toward sovereign AI infrastructure.
Why Adversarial Attacks Are an Enterprise Biometric Threat
Sophisticated attacks using adversarial patches or digital perturbations can fool state-of-the-art face and iris recognition systems, demanding red-teaming in the SDLC.
How AI-Powered Microexpression Analysis Fails Cross-Culturally
Emotion recognition models trained on biased datasets perform poorly across demographic groups, creating ethical risks and security blind spots.
Partnered with leading AI, data, and software stack.
How We Work
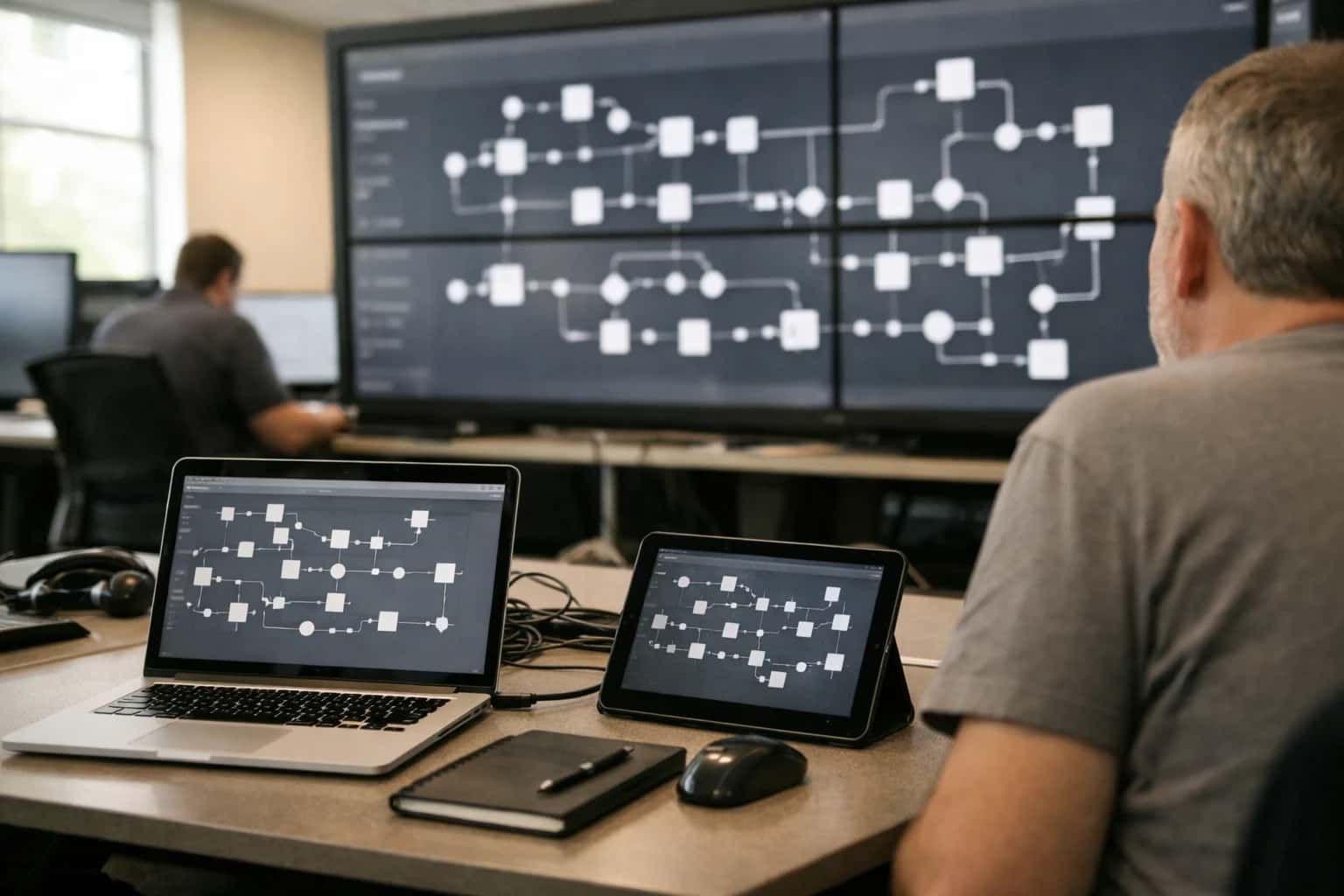
Custom AI workflows for your Business
One-fit-all AI don't work for modern businesses. At Inferensys, we aim to understand your business & custom requirements; which we use to define most efficient agentic workflows, the data, and the tools for your business.
01
Review the use case
We understand the task, the users, and where AI can actually help.
Read more02
Pick the right approach
We define what needs search, automation, or product integration.
Read more03
Build the first useful version
We implement the part that proves the value first.
Read more04
Improve from there
We add the checks and visibility needed to keep it useful.
Read moreThe first call is a practical review of your use case and the right next step.
Talk to Us